Pick Your Battles with Identity Deception
The global economy in 2026 is transitioning to the full digitalization of goods and services, and the gap between a fraudster’s technological toolkit and a company’s defensive methodology is widening at an industrial scale. While data spoofing and human engineering have become highly sophisticated, many organizations are still fighting 21st-century exploits with 20th-century enforcement.
This column, The Mitigation Lab, will deconstruct the most sophisticated fraud MOs across fintech, e-commerce and gaming from a data science perspective. Each month, I will break down the ‘Exploit’—the pain of emerging schemes—and provide the ‘Enforcement’—the data-driven methodologies and detection tools you need to stay ahead of the curve.
Every column will move past industry jargon to offer actionable insights on how to invest in your data and enhance your detection tools to protect the bottom line. However, let’s start at the beginning.
Ms. Focus
I’m usually brought in as a consultant when fraud risk has become strategically uncomfortable for companies — not because controls have failed, but because it’s unclear where to focus. Deception is everywhere: from AI-generated identities, scalable spoofing infrastructure to increasingly human-like automation.
Companies face a dilemma: strengthen every control and place their growth at risk, or accept ambiguity and tolerate exposure to fraud risk.
The instinct is to verify everything. In reality, that approach isn’t sustainable. Identity deception operates at an industrial scale, and layering controls indiscriminately increases vendor costs, false positives, and customer friction — sometimes exceeding the fraud losses themselves.
The more durable strategy is disciplined prioritization: identifying which forms of deception materially threaten your model and concentrating resources there.
Fraudsters Optimize for Acceptance
Modern fraud is less about intrusion and more about assimilation. The fraudsters want to be scored as your ideal customer.
Jurisdictional mimicry is common. Attackers align IP reputation, device signals, and declared location to appear within approved markets.
Demographic masking follows the same logic. Risk models apply different friction to different segments, so declared attributes shift accordingly. A 19-year-old high-frequency bettor becomes a 42-year-old professional.
Identity multiplication adds scale. One actor becomes hundreds of plausible accounts. Each passes an isolated review. Only in aggregate — shared device artifacts, synchronized activity windows, overlapping behavioral signatures — does coordination emerge.
Automation is now engineered to look human. Scripts introduce hesitation, cursor drift, even small “mistakes.” Fraud adapts to whatever your models reward.
Deception as Configurable Infrastructure
What distinguishes the current environment is accessibility:
- Autonomous agents navigate onboarding flows and adjust responses dynamically.
- Emulated mobile environments simulate real devices while suppressing unwanted security signals.
- Generative models produce convincing documents and facial imagery that challenge basic verification workflows.
- Residential proxy networks provide IP footprints indistinguishable from legitimate households.
Fraudsters test acceptance thresholds the way growth teams test conversion funnels — iteratively and with data.
An Expanding Defensive Ecosystem
Fraud prevention technology is evolving rapidly as well— and that is a good thing.
- Industry-wide intelligence networks detect behavioral patterns across platforms (Forter, SEON, Equifax).
- Device attestation solutions verify application integrity at the hardware level (Approve, Appdome,Zimperium).
- Location intelligence providers reconcile inconsistencies across GPS, IP, Wi-Fi, and network routing signals (IpInfo, IPQS, MaxMind).
- Behavioral analytics engines detect automation disguised as human interaction (HumanSecurity, BioCatch, BehavioSec)
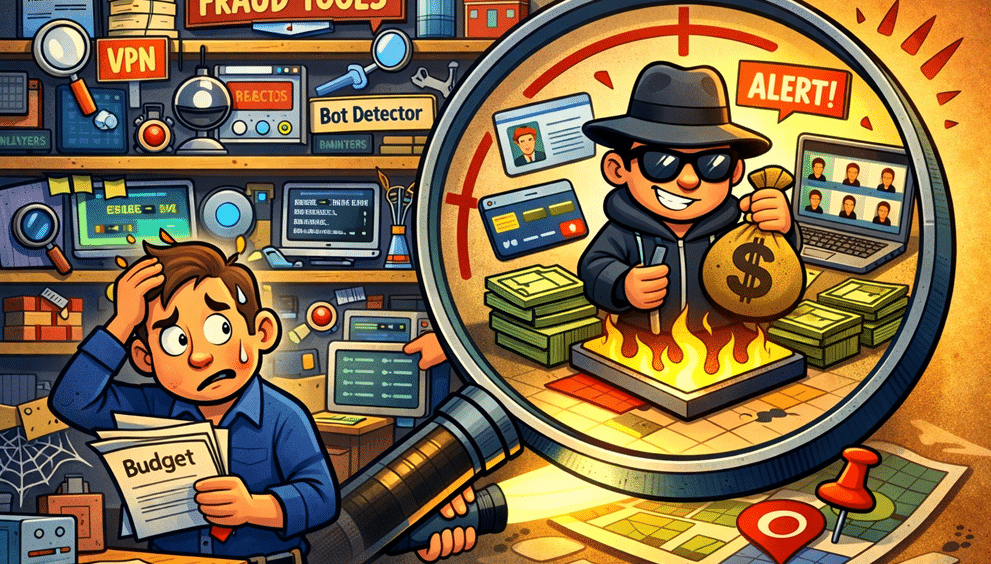
The challenge is not scarcity of tools, but abundance.
Each additional layer improves signal quality. Yet no organization can deploy every available solution without incurring significant cost and operational complexity. Overlapping vendors, integration burdens, and diminishing returns become real constraints. The strategic question is no longer “What can we detect?” but “Which investments meaningfully reduce our fraud risk exposure?”
Choosing What to Fight
No organization has unlimited investigative capacity. Every control introduces cost — financial, operational, or experiential.
The strategic task is segmentation:
- Which identity failures create regulatory liability?
- Which risk materially impacts capital or liquidity?
- Which are economically tolerable within defined thresholds?
Treating all fraud vectors as equally urgent often produces more friction than protection. Prioritization is crucial; focus efforts where they will have the greatest impact.