The 5 Step AML Intelligence Cycle
Anti-money laundering (AML) professionals are often heard to lament filing piles of Suspicious Activity Reports (SAR) that go into a proverbial black hole, never to be seen or heard from again. I may have lent my voice to that chorus over the years as well. A SAR is the result of an AML investigation where someone found activity that was odd enough to report to the US government via the Financial Crimes Enforcement Network (FinCEN; Outside the US this is often known as a Suspicious Transaction Report (STR). It is true that the SAR database is not accessible to everyone, and that it contains massive amounts of data that may never prove useful. However, the art of AML intelligence is in finding and placing puzzle pieces, not necessarily in making a single discovery that causes a breakthrough in fighting crime.
Applying an intelligence mindset to AML helps bring the volume of SAR information into perspective. First, intelligence in this context refers to analyzed, potentially actionable information gathered in response to a management query. Broadly, intelligence sources are often characterized by their collection source. Imagery from satellites is called “IMINT” while signals from phone and radio communications are called “SIGINT”. Information from financial institutions, reported via SARs, should be called “FinINT”. It is one of many collection sources available to law enforcement, military, and other government agencies for fighting crime, terrorism, and threats to national security.
When working on a jigsaw puzzle, one does not always pick up a piece and immediately know its place in the larger picture. Writing a common SAR is like discovering a puzzle piece far from the rest of the puzzle, inexplicable except in that it is likely to fit with other puzzle pieces somewhere. A simple report involving customers “structuring” cash deposits below $10,000, or removing money to avoid cash reporting requirements, a description of an uncomfortable customer with unexplainable International wires, these can confirm leads or identify suspects for law enforcement in cases that do not make the news. Just because we cannot explain the puzzle piece’s role in the larger picture does not make it unimportant.
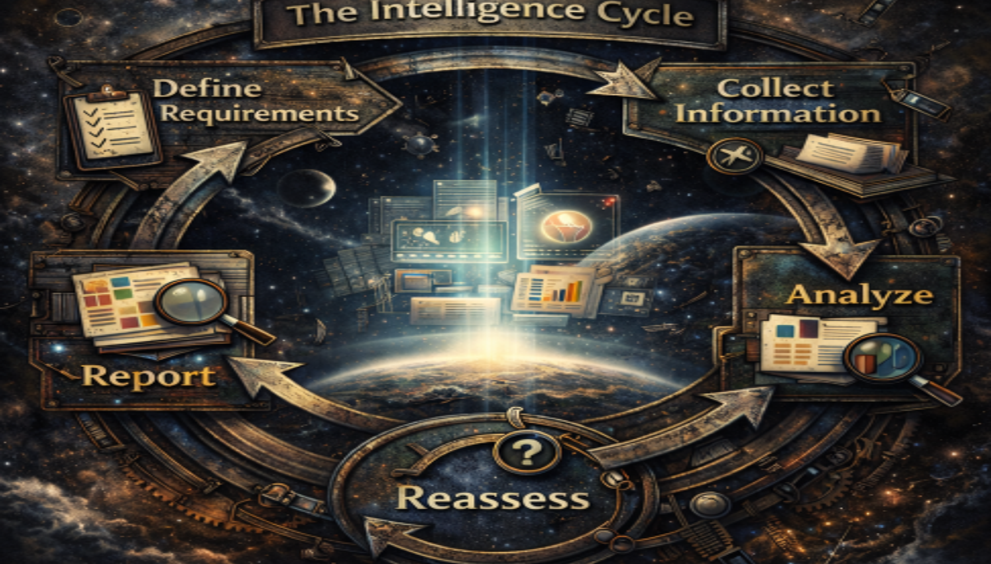
With such a large volume of financial information going to FinCEN in the form of SARs every year, meta-analysis also identifies suspicious activity across financial institutions. This is highly valuable in the right hands, with savvy data analytics. Yet, how do we get from a massive trove of information to useful, analyzed, actionable intelligence? The answer lies in the military and national security world’s characterization of the process as a cycle with several steps. While agencies define the steps differently, here is a model applying the most common steps to the AML workflow and investigative process:
Defining Requirements
What question needs to be answered? Financial institutions are legally charged with having a system for identifying unusual activity that could be related to money laundering or terrorism financing. This requires a full-spectrum risk analysis that leads to a variety of policy, training, monitoring, and due diligence efforts. There are a lot of lines of questions to be explored inside of each of those tasks, but once a relationship and set of transactions appears at an investigator’s desk as a case it becomes a dichotomy: is the activity suspicious enough to report, or not? That question leads the rest of the collection effort.
Collecting Information
This is the process of gathering information from various sources. Inside a financial institution, this usually consists of internal records, paid information sources, and open-source records. All available sources should be considered for investigative subjects, and investigators must be careful to ensure they are researching the right customer and not someone different but of the same name.
Investigators will review transaction information, customer due diligence records, check images, and more to understand how the customer uses the institution compared to who or what they seem to be. Internal records are compared with data from the internet, secretary of state, post office, motor vehicle department, or other publicly available information.
AML Intelligence Analysis
Analysis takes place during and after collecting information. While collecting information, investigators are constantly evaluating the validity of sources, accuracy of data, and implications of the activity. Cross-referencing public information with internal records is a powerful way to understand intent and recognize unusual or mismatched behavior. Analysts must be careful to consider the age of information, especially if financial institution records are not updated regularly for all relationships.
At this phase, investigative analysts begin to develop a theory on whether account and transaction activity make sense or seem suspicious. When unsure, it is advisable to make a list of supporting evidence for the competing hypotheses and see which answer is more difficult to support. Often the facts speak for themselves.
Reporting & Dissemination
All good reports consider the audience. Investigators should use common language, spell out acronyms, and explain internal processes when needed. Institutions should have a reporting format, and good programs use report formats familiar to the law enforcement and intelligence communities. Investigators should mention both fact and analytical opinion, and be clear on the difference between the two.
Sometimes, filing required reports is not enough. When high risk or high priority cases come to light, it is important to maintain contacts with regulators and law enforcement agencies. Personal connections help move along important intelligence, even if the message is only to read a certain SAR narrative as soon as possible.
Reassessment of AML Intelligence Requirements
Lastly, investigators should make a short note of case typologies that seem common or stand out as unusual. Management must be regularly reviewing cases for trends as well as reevaluating risk assessments, policies, and detection models to capitalize on lessons learned. Each member of the team must remain well informed of the latest trends, typologies, and techniques of criminal networks in order to detect and report related activity.
At every level, the funnel that reviews transaction activity for what is ultimately reported as suspicious must be tuned and constantly reassessed. Regulatory requirements and expectations change, as do economic conditions, financial products, criminal tactics. The diverse nature of knowledge required urges us to constantly assess and update our understanding of what is required to report and thereby fight financial crime.